原贴地址:[实战]利用传智播客旗下黑马程序员培训学生用的博学谷系统撞库批量拿个人资料
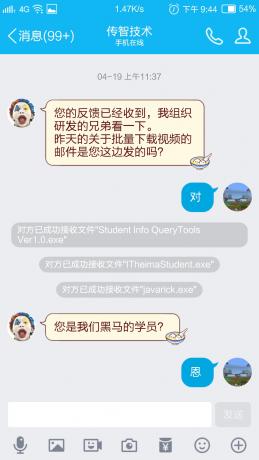
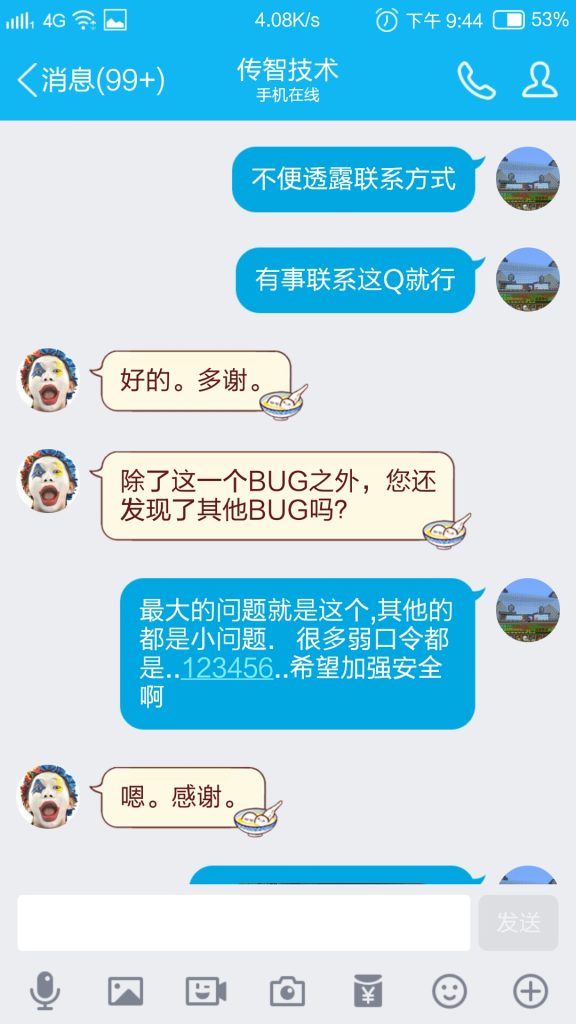
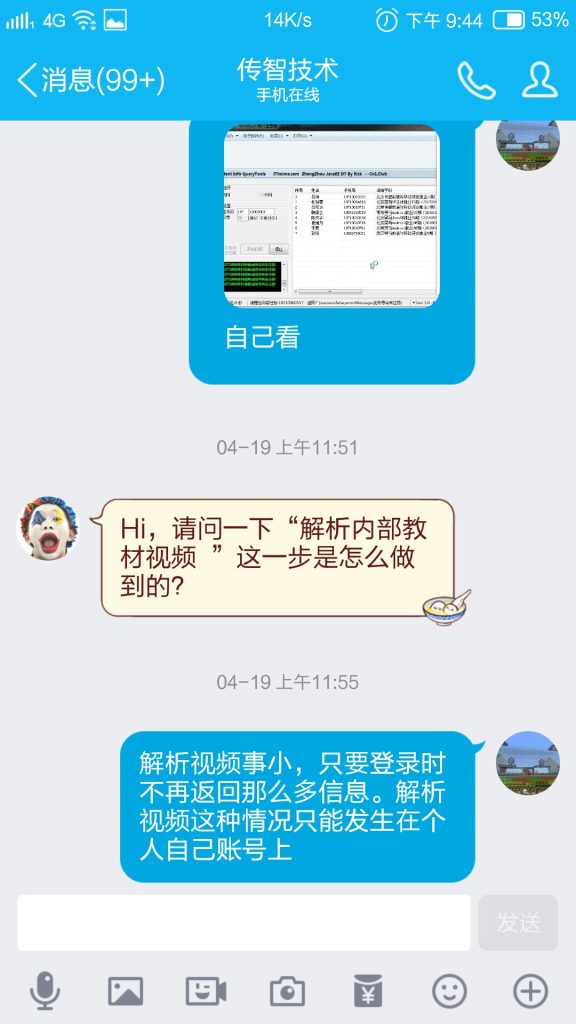
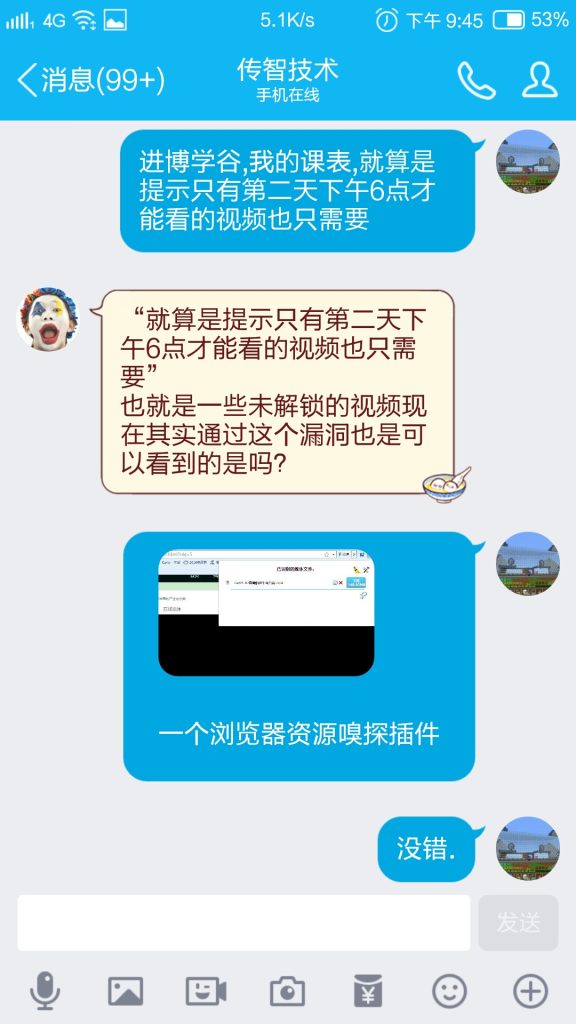
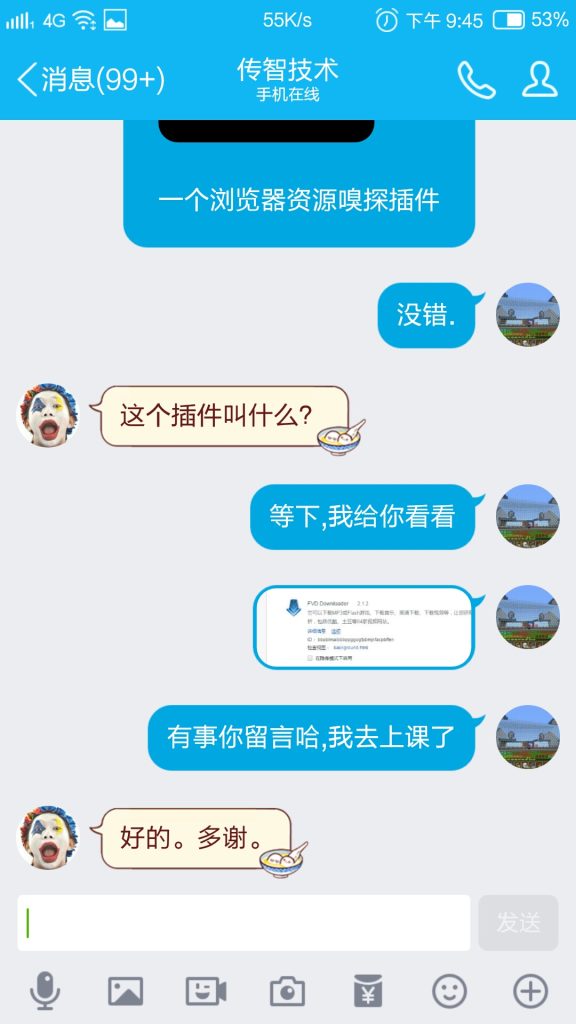
沟通进程:
最新进展:
2017/04/14 发现漏洞
2017/04/15 继续挖掘漏洞,发现此漏洞为全国性质,各地区学员隐私信息均可查看,学分,神分证号,学号,手机QQ号,邮箱,学历...等
2017/04/16 发现全国各地学员密码均为123456弱密码,登录博学谷可以拿到未加密版的黑马各个版本各个学科就业班视频,已经取得办法解析到原视频...毕竟自己得信息也同样在光着腚跑,想想还是提交算了..
2017/04/17 突发想法,写出多线程手机H递增遍历工具,拿到了一些信息..
2017/04/19 提交漏洞给官方了...(哎..有点后悔啊,这些视频拿下来卖淘宝我不就小赚一笔了)
2017/05/21 官方已修复漏洞,当检测到学员使用12356口令登入时提醒其改密码才能进入,POST提交地址的漏洞已修复.
2017/08/12 漏洞实测有办法绕过限制,目前对部分漏洞信息作隐藏处理!
漏洞信息:
2017/08/12
[具体方式因此漏洞或复发!现已隐藏!]
[具体方式因此漏洞或复发!现已隐藏!]
Get到一串返回过来的字符串,JSON格式,格式化以后(隐私数据已打*):
{
"success": true,
"resultObject": {
"studentNo": "052",
"workYear": 0,
"classInfo": {
"schoolId": "8a9969bc56cb285b0156f85fa6a011e6",
"brandId": "1",
"subjectId": "ff808081528b0ee201528b201da60003",
"classType": 0,
"classType1": "1",
"className": "XX黑马JavaEE就业X期(201703XX双元)",
"classPeriods": "7",
"headMaster": "8a9969bc58712a730158ae24c90d2cb3",
"seatStatus": false,
"startDate": "Mar 23, 2017 12:00:00 AM",
"endDate": "Apr 5, 2017 12:00:00 AM",
"ruleOn": 2,
"ruleOff": 1,
"ruleOn1": 2,
"ruleOff1": 1,
"examScore": 83.98,
"id": "8a99d62d5ab2307a015adba726b11685",
"isDelete": false,
"createPerson": "8a99d62d5850f48d0158520f9d0f0235",
"createTime": "Mar 17, 2017 5:44:09 PM"
},
"studentGroup": {
"groupName": "默认",
"id": "1",
"isDelete": false
},
"fee": 0,
"studentType": 0,
"isRight": 0,
"schoolStudentType": "系统升班",
"firstLoginSign": "1",
"studentStatus": 1,
"forbidStatus": 0,
"talkTimes": 0,
"education": "大X",
"name": "赵X",
"loginName": "1366XXXX358",
"password": "",
"sex": 1,
"mobile": "1366XXXX358",
"id": "8a9969bc5ae0b56a015aefa885d743a9",
"isDelete": false,
"createPerson": "8a9969bc58712a730158ae24c90d2cb3",
"createTime": "Mar 21, 2017 2:58:03 PM"
}
}
=====================
遍历手机号可以拿到更多数据,最后批量撞库筛选出有效可登入的号码,进而利用学员的学科下载就业班的视频.